Firewall Analyzer
 Firewalls have become an integral part of all corporate networks. They’re the first line of defense against attacks from outside network (Internet) and also the point of control to make sure internal users (employees) are using the Internet as they’re supposed to. Recently the UTM (United Threat Management) Firewalls have become very popular. They’ve built in gateway anti-virus, anti-spam, web content filtering and IPS (Intrusion Prevention System) on top of traditional firewall functions. These firewalls generate loads and loads of log data and it’s very difficult to analyze the traffic and security event levels by just looking at the log files. So, a firewall logging and analyzing tool becomes necessary to generate easy to understand reports. After trying few softwares, I came across Firewall Analyzer, which was the exact tool I was looking for.
Firewalls have become an integral part of all corporate networks. They’re the first line of defense against attacks from outside network (Internet) and also the point of control to make sure internal users (employees) are using the Internet as they’re supposed to. Recently the UTM (United Threat Management) Firewalls have become very popular. They’ve built in gateway anti-virus, anti-spam, web content filtering and IPS (Intrusion Prevention System) on top of traditional firewall functions. These firewalls generate loads and loads of log data and it’s very difficult to analyze the traffic and security event levels by just looking at the log files. So, a firewall logging and analyzing tool becomes necessary to generate easy to understand reports. After trying few softwares, I came across Firewall Analyzer, which was the exact tool I was looking for.
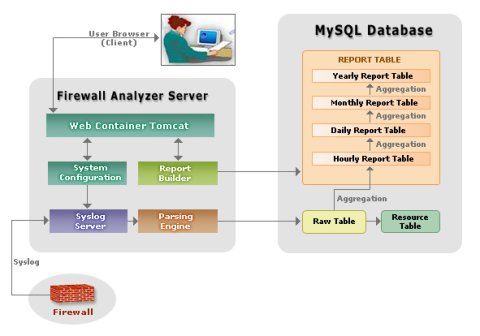
Architecture
Firewall Analyzer is a web based firewall log analysis tool. It has a built-in syslog server to store the logs and comes with an integrated and pre configured MySQL database.
Firewall Compatibility
Firewall Analyzer is compatible with most of the popular firewalls like Cisco PIX, Netscreen, Watchguard, Sonicwall, Check Point and many more… , some of them have configuration instruction as well. I’ve configured mine with the Netscreen firewall.
System Requirements
Minimum hardware requirements for installing Firewall Analyzer is:
1GHz Pentium 4 processor or equivalent
512 MB of RAM
1 GB of disk space
Monitor that supports 1024×768 resolution
RAM and disk space requirement depends upon the number of devices you’re logging. They’ve more information on MySql performance improvements and suggestion for RAM and Hard Disk size for different number of devices.
Installation
I’ve installed it in a Linux Server (CentOS 4.x). All you need to do is execute ./ManageEngine_FirewallAnalyzer.bin. I think it should be fairly easy to install in the Windows too. But why would anyone buy an extra windows license, if it can be done in Linux, which is much secure and stable than Windows 🙂
Configuration
The configuration is pretty straight forward. After the installation, you should start the service by executing run.sh. By default the run script is installed here:
/root/AdventNet/ME/Firewall/bin/run.sh
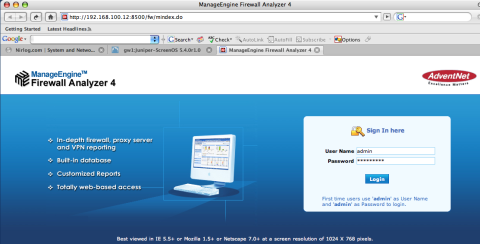
The firewall analyzer can now be accessed from a browser by typing:
http://<hostname>:8500
The default username/password are admin/admin, which can be changed after logging in.
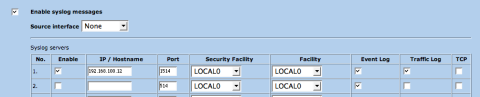
You need to configure your firewall and point the logging to this server’s ip with the port number it’s listening to. It uses udp port 514 and 1514 by default. In Netscreen firewall, it can be done by going to: Configuration > Report Settings > Syslog
Features
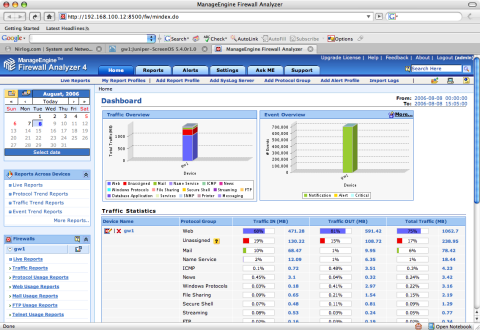
- Enterprise-wide View of Network Activity
- On-Demand and Real-time Reports
- Scheduled Log Archiving
- Advanced Data Analysis and Reporting
- Support for most Leading Firewalls
- Historical trending
- Real-time, Threshold-based Alerting
- Virus, Attack and Security Analysis
Firewall Analyzer helps to analyze the traffic/bandwidth patterns, identify top users, determine bandwidth usage by hosts, protocols and destinations, generate alerts on specific events, identify potential virus or hack attacks and many more…
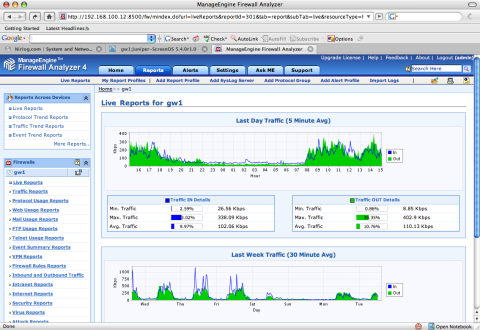
You can visit the live demo site to see Firewall Analyzer in action and if you want to try it for yourself, then fully functional 30 day trial software is available for download. The pricing scheme is based on annual subscription, starting at USD 295/year for 1 device pack.
Firewall Analyzer gives you a bird’s-eye view of your network traffic and is a very useful productivity tool to help identify and troubleshoot network problems. I think it’s fully worth it’s price.





Recent Comments